
Artificial Intelligence (AI) and Machine Learning (ML) require a lot of computing power. Specifically, you would want to have GPUs which have become the standard tool for computing-intensive applications because of their parallel processing capabilities, high throughput, and efficiency in handling the kinds of large-scale computations required for AI and ML.
Read More
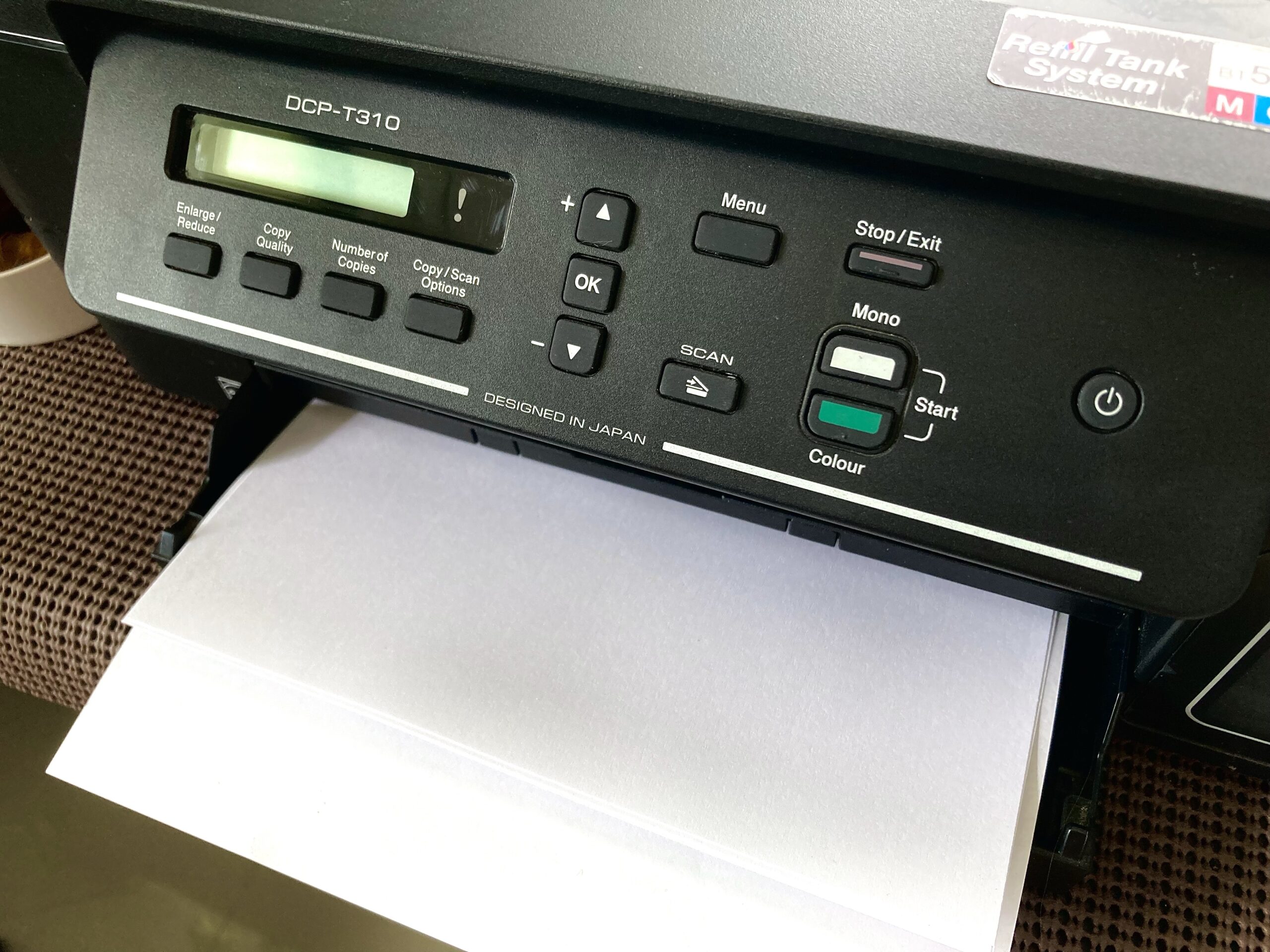 Setting up a print server allows you to share your regular USB printer as a network printer. We can set it up to allow printing using AirPrint from iOS and MacOS devices. We can even set it up to allow printing from Windows devices. Let’s set up one with a basic Raspberry Pi W. Of course, the higher Pis would do as well.
Setting up a print server allows you to share your regular USB printer as a network printer. We can set it up to allow printing using AirPrint from iOS and MacOS devices. We can even set it up to allow printing from Windows devices. Let’s set up one with a basic Raspberry Pi W. Of course, the higher Pis would do as well.