
If you’ve been around a while, you’d remember there was a time when you can rest quietly assured that your Linux box is safe from viruses and other malware. Or rather, few bad actors bother to target Linux. Most target Windows. That was then. But today, with the increase in the popularity of Linux not just on servers but even on desktops, Linux is no longer under the radar of bad actors.
So a few days ago, I was alerted to abnormal CPU utilization on one of my servers. I logged in to check and saw that there’s a process called perfctl that was using up CPU time. I killed it but it respawned after a while. It looked like my Linux server had malware.
Read More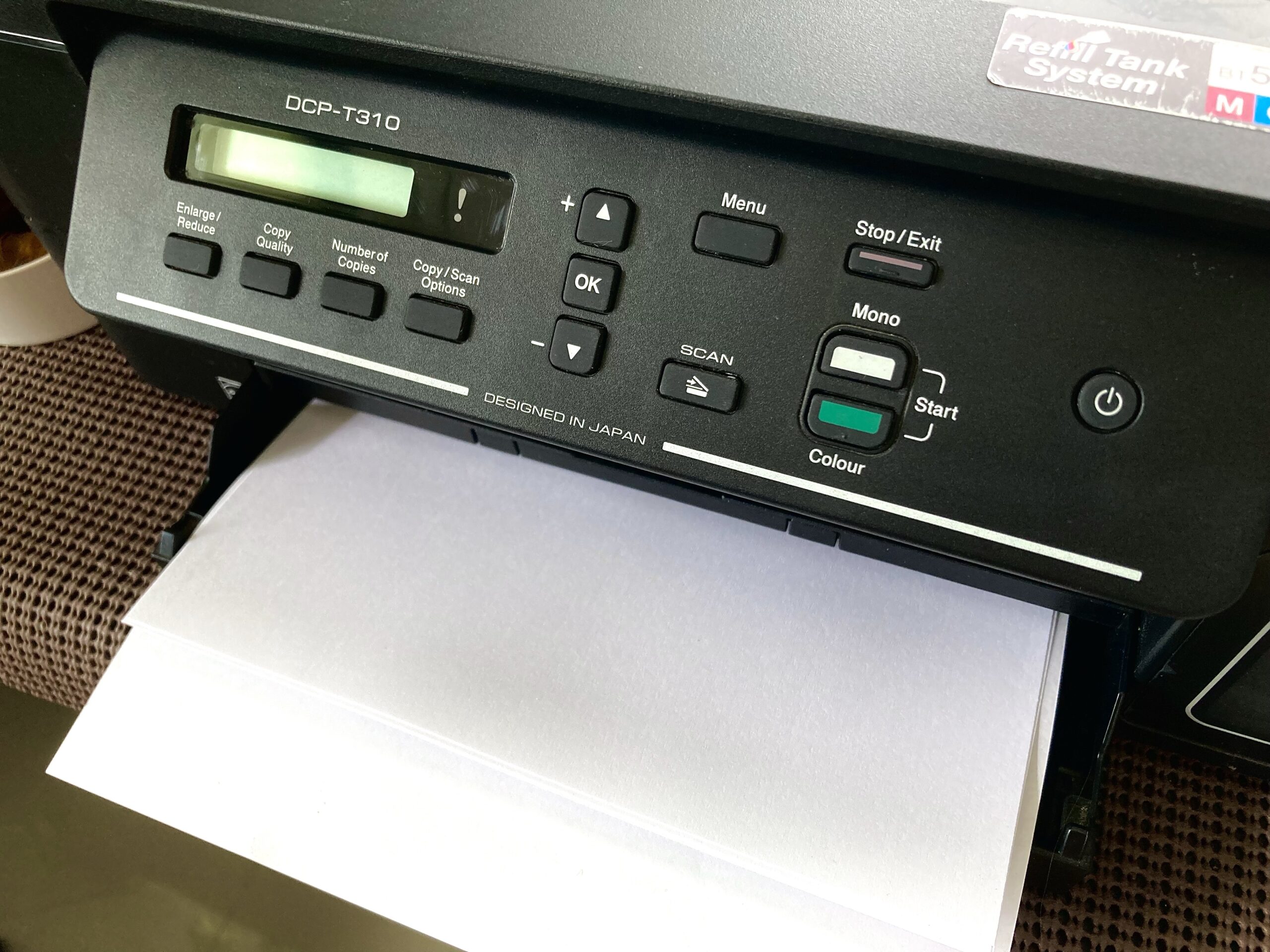 Setting up a print server allows you to share your regular USB printer as a network printer. We can set it up to allow printing using AirPrint from iOS and MacOS devices. We can even set it up to allow printing from Windows devices. Let’s set up one with a basic Raspberry Pi W. Of course, the higher Pis would do as well.
Setting up a print server allows you to share your regular USB printer as a network printer. We can set it up to allow printing using AirPrint from iOS and MacOS devices. We can even set it up to allow printing from Windows devices. Let’s set up one with a basic Raspberry Pi W. Of course, the higher Pis would do as well.